【Python黑帽子】——搭建TCP端口扫描器
经过一段时间python黑帽编程的学习,我们的漏洞扫描器搭建之旅就要开始了,最开始当然要做的就是端口扫描器,所以这篇博客我们的内容就是搭建一个TCP扫描器,来看看吧
代码如下
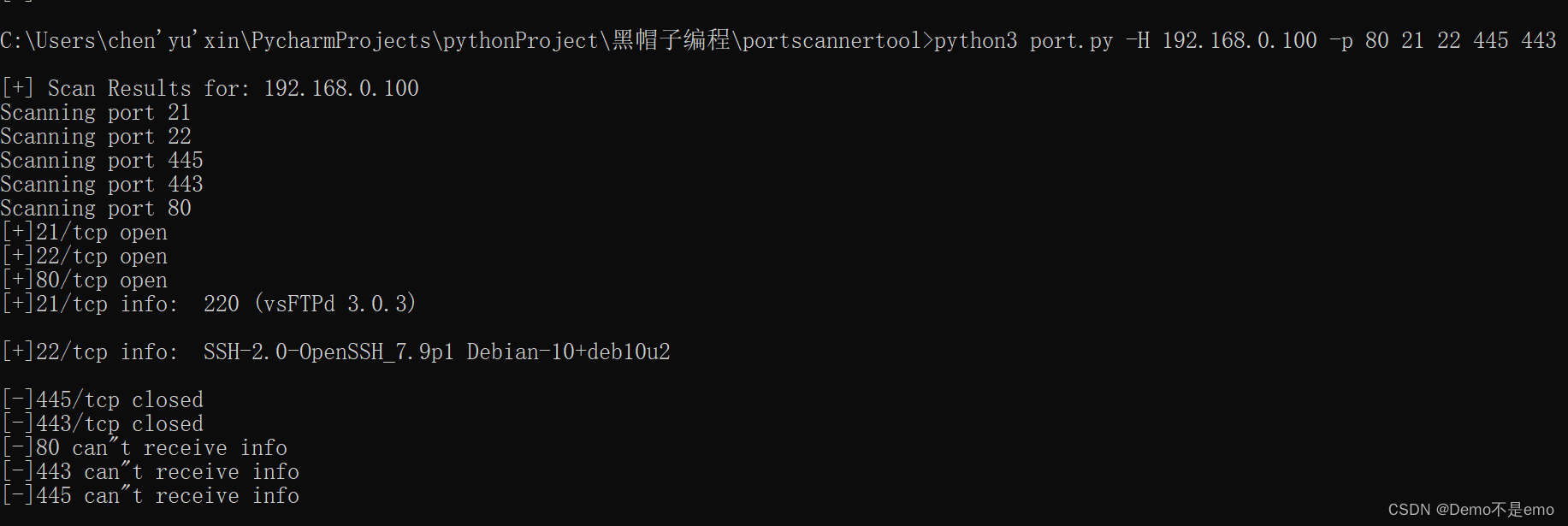
# coding=UTF-8 import optparse import socket import threading screenLock = threading.Semaphore(value=1) def connScan(tgtHost, tgtPort): try: connSkt = socket.socket(socket.AF_INET, socket.SOCK_STREAM) connSkt.connect((tgtHost, tgtPort)) print('[+]%d/tcp open' % tgtPort) except Exception: print('[-]%d/tcp closed' % tgtPort) try: # connSkt.send('ViolentPython/r/n') results = connSkt.recv(1024).decode("UTF-8") screenLock.acquire() print('[+]%d/tcp info: ' % tgtPort + str(results)) except Exception: screenLock.acquire() print('[-]%d can"t receive info' % tgtPort) finally: screenLock.release() connSkt.close() def portScan(tgtHost, tgtPorts): try: tgtIP = socket.gethostbyname(tgtHost) except Exception: print("[-] Cannot resolve '%s': Unknown host" % tgtHost) return try: tgtName = socket.gethostbyaddr(tgtIP) print('/n[+] Scan Results for: ' + tgtName[0]) except Exception: print('/n[+] Scan Results for: ' + tgtIP) socket.setdefaulttimeout(1) for tgtPort in tgtPorts: print('Scanning port ' + str(tgtPort)) t = threading.Thread(target=connScan, args=(tgtHost, int(tgtPort))) t.start() def main(): parser = optparse.OptionParser('usage %prog –H<target host> -p <target port>') parser.add_option('-H', dest='tgtHost', type='string', help='specify target host') parser.add_option('-p', dest='tgtPort', type='int', help='specify target port') (options, args) = parser.parse_args() tgtHost = options.tgtHost tgtPort = options.tgtPort args.append(tgtPort) if (tgtHost is None) | (tgtPort is None): print('[-] You must specify a target host and port[s]!') exit(0) portScan(tgtHost, args) if __name__ == '__main__': main() 效果展示
这个端口扫描器有两个作用,
这个代码拿去就可以用,同时也在我的github和gitee上更新了 ,里面还附带有详细的用法说明,工具后面也会不断更新,欢迎持续关注
Gitee地址:PortScan_pro: TCP端口扫描器加强版 (gitee.com)
版权声明:本文内容由互联网用户撰写,该文观点仅代表作者本人。本站爱分享仅提供分享服务,不拥有所有权,不承担相关法律责任。如发现本站有涉嫌抄袭侵权/违法违规的内容,请立马联系本站,本站将立刻删除。
THE END
二维码
共有 0 条评论